Securing Digital Systems: Hardware Perspectives
In an increasingly interconnected world, the security of digital systems is paramount. While software vulnerabilities often capture headlines, the underlying hardware components form the bedrock of any secure computing environment. Understanding how processors, memory, storage, and other physical elements contribute to or compromise system integrity is crucial for building resilient digital defenses. This article explores the various hardware perspectives involved in safeguarding modern technology, from the smallest microchip to complex network infrastructures, emphasizing the foundational role of physical components in overall security.
Digital systems are integral to modern life, impacting everything from personal communication to critical infrastructure. The emphasis on securing these systems often defaults to software solutions, but robust security begins at the hardware level. The physical components of any computing device or network system present unique challenges and opportunities for defense against various threats. A holistic approach to digital security must consider the intrinsic properties and vulnerabilities of hardware, from its design and manufacturing to its deployment and end-of-life.
The Foundation of Security: Processors and Microchips
At the core of every digital system lies the processor, often a complex microchip responsible for executing instructions and managing data flow. The security of these fundamental components is paramount. Modern processors incorporate features designed to enhance security, such as secure boot mechanisms that verify the integrity of firmware before it loads, preventing tampering. Trusted Platform Modules (TPMs), often integrated into or alongside processors, provide hardware-based cryptographic functions and secure storage for sensitive data like encryption keys. These devices create a root of trust, ensuring that the system starts in a known, secure state. Threats like side-channel attacks, where adversaries analyze power consumption or electromagnetic emissions to infer secret data, highlight the ongoing challenge in designing truly secure microchips and processors, driving continuous innovation in their engineering.
Data Integrity: Securing Storage and Memory Devices
Data is the lifeblood of digital systems, and its protection, both at rest and in transit, is critical. Storage devices, such as solid-state drives (SSDs) and hard disk drives (HDDs), are primary targets for data theft. Hardware-level encryption, often built directly into these devices, provides a robust layer of defense, making data unreadable without the correct cryptographic key. Similarly, memory components like RAM, while volatile, are susceptible to attacks that aim to extract sensitive information during system operation. Techniques such as memory encryption and secure memory regions help protect data while it is actively being processed. The integrity of both storage and memory is essential for maintaining the confidentiality and availability of information within any computing device or broader digital system.
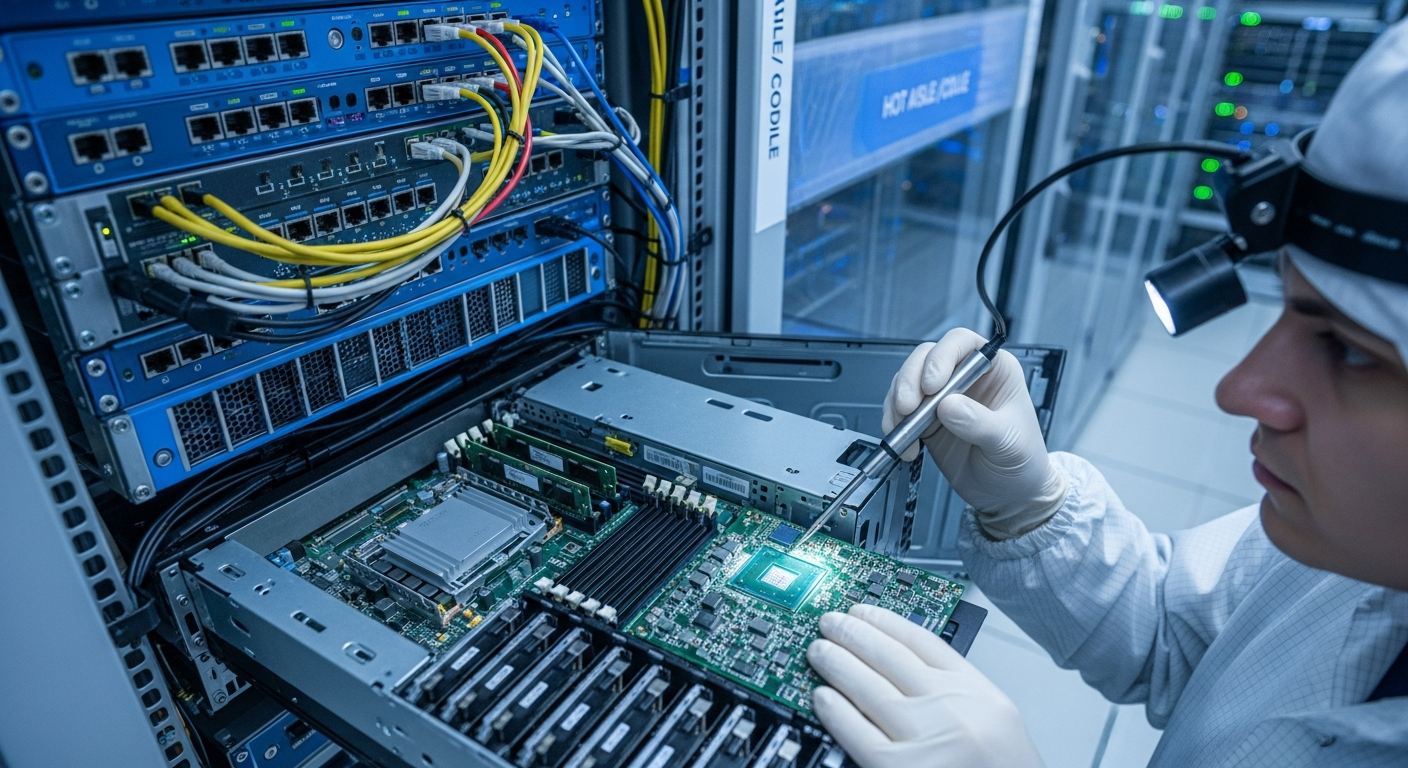
Hardware Components in Network and System Protection
Beyond individual devices, the security of entire networks and systems relies heavily on their hardware components. Network devices such as routers, switches, and firewalls are purpose-built hardware components that form the backbone of digital communication. Their firmware and underlying hardware must be secure against tampering to prevent unauthorized access or data interception. Specialized hardware accelerators can offload cryptographic operations, improving performance without compromising security. Furthermore, physical security measures for servers and computing infrastructure, including secure enclosures and access controls, are fundamental. The reliability and integrity of these various hardware components are essential for maintaining the overall security posture of complex digital networks and systems, often requiring careful engineering and maintenance.
Advancements in Secure Hardware Engineering and Innovation
The landscape of digital security is constantly evolving, driven by ongoing innovation in hardware engineering. Researchers and engineers are developing new approaches to design and manufacture more resilient components. This includes the exploration of intrinsically secure architectures, such as physically unclonable functions (PUFs) that provide unique, uncloneable identifiers for microchips, enhancing device authentication. Supply chain security for hardware is another critical area, ensuring that components are authentic and free from malicious modifications from manufacturing to deployment. Advances in materials science and fabrication techniques also contribute to creating more robust and tamper-resistant hardware. The continuous pursuit of secure hardware engineering aims to embed security deeply into the very fabric of digital technology, making systems inherently more trustworthy.
The Future Landscape: Automation in Digital System Security
Looking ahead, automation is set to play an increasingly significant role in enhancing the security of digital systems at the hardware level. Automated tools can be used in the design verification process to identify potential vulnerabilities in microchips and other components before they are manufactured. During deployment, automated monitoring systems can detect unusual hardware behavior that might indicate a security breach or a component failure. Furthermore, advancements in automated threat response could enable systems to isolate or neutralize compromised hardware components dynamically, minimizing potential damage. The integration of artificial intelligence and machine learning with hardware security mechanisms promises to create more adaptive and resilient computing environments, capable of proactively defending against sophisticated threats across diverse digital devices and systems.
In conclusion, securing digital systems requires a comprehensive approach that extends far beyond software. The intricate world of hardware, encompassing processors, memory, storage, and various other components, forms the fundamental layer of defense. By focusing on secure design, manufacturing, and deployment of these physical elements, combined with continuous innovation and the strategic use of automation, the overall resilience and trustworthiness of our interconnected digital world can be significantly enhanced. Understanding the hardware perspective is not just beneficial; it is indispensable for building truly secure computing environments.






